The lack of cyber security talent is well documented. Organisations have responded in various ways, with many of them opting to plug the supply gap by leveraging elements of an external monitoring service, such as a security operations centre (SOC) or managed detection and response (MDR) provider.
These third parties provide capacity and expertise and form a critical component of cyber security within an organisation’s control framework. But resource constraints can lead to a lack of oversight, and testing of these services presents a significant risk to businesses.

There are many benefits to leveraging such a service, but providers often operate quietly in the background and give their clients limited insights into just how effectively their services are running. Instead, they usually present abstract KPIs in a manner that can result in false confidence in the service’s effectiveness.
Our experience has shown us that these critical services are frequently misconfigured and do not operate as desired. The broader business impact is that the investment is, essentially, under optimised. In terms of risk management, however, an organisation’s cyber risk significantly increases, and it is presented with an additional, unmanaged level of risk. This could occur for many reasons:
- If unmanaged, a natural shift in the client’s technology landscape could result in a misalignment between the business requirements and the service that was procured.
- A de-prioritisation of existing clients may result in an accumulation of technical debt that fails to bring the benefits that the service originally promised.
- A comparison can be drawn between other business models in which the focus is growth. Once a subscription is secured, there is a gradual drop in the level of service as the financial incentive to provide continued value to the client is reduced.
- The role of legacy MDR infrastructure must not be overlooked. A key part of these procured services is often the introduction of bridging infrastructure that provides mechanisms for supporting the delivery of the services. As with any other technology, mismanagement of this technology can lead to the growth of technical debt.
- A failure to operationalise and contextualise threat intelligence effectively within a SOC provider could mean appropriate alerts are not generated in response to the emerging threats.
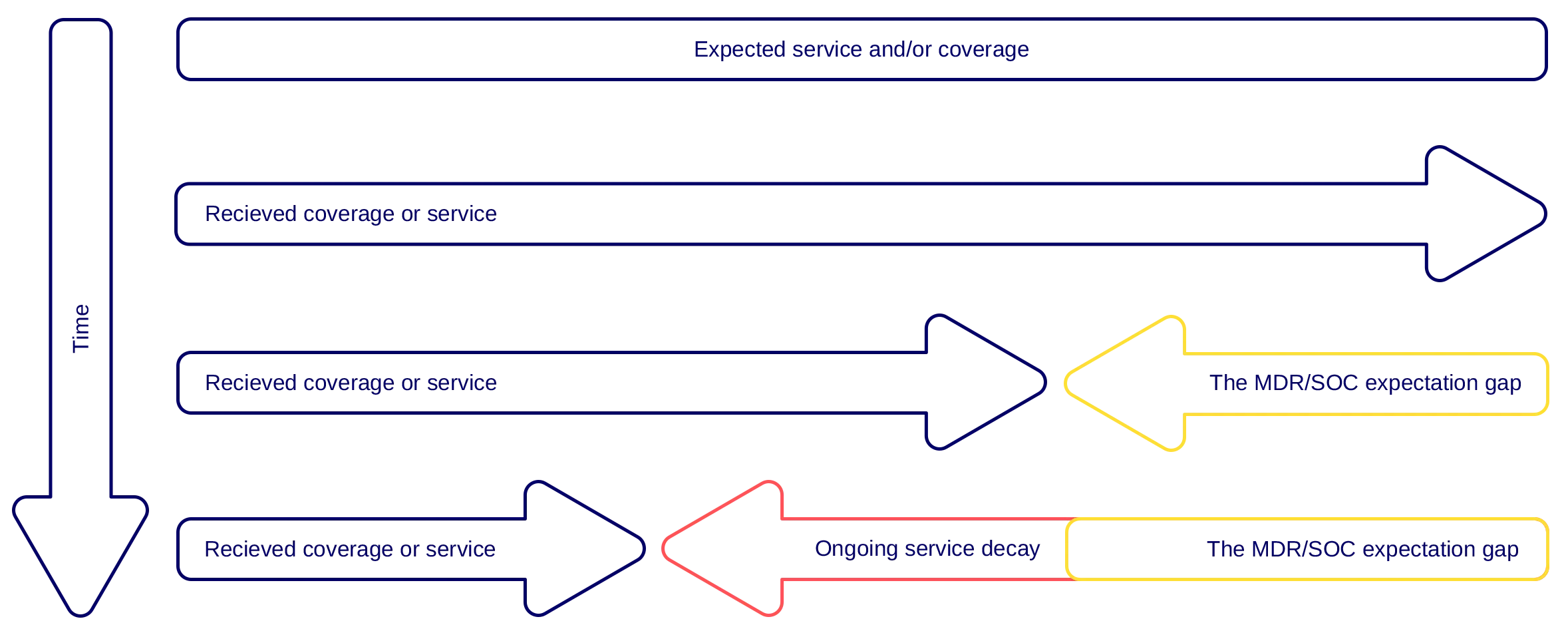
Our team regularly needs to provide forensics and incident response assistance where a third-party is already providing an MDR service, and the service provider has either not detected a threat or failed to respond appropriately to one. This is something we have coined the “MDR expectation gap.” This expectation grows over time as the ongoing service decay continues to impact the coverage, and thus increase the risk facing the business.
At Thomas Murray, we recognise the importance of addressing the expectation gap as well as optimising the significant investment organisations make in these external services.
We have developed a service that provides insights into this critical area by leveraging our experiences of:
- working for large SOC/MDR providers;
- working with incident responders on hundreds of incidents; and
- working as threat intelligence leads and CISOs.
We enable clients to identify and address issues in a proactive manner, for example before a breach occurs.
Thomas Murray’s approach allows us to:
- Test the deployment of MDR and SOC services by ensuring the collection and aggregation of logs from critical sources across the monitored environment.
- Validate the response and effectiveness of the operational elements of an SOC and/or outsourced service by systematically triggering alerts.
- Work in conjunction with an internal team and provide targeted education for SOC teams to improve their detection capabilities, allowing for a refinement of their alerting mechanisms and optimise processes.
- Optimise the client’s investment in the SOC/MDR service and ensure contractual SLAs are being met.
| Case study | |
| Client profile | A leading global law firm. |
| Situation and solution | The Thomas Murray team helped address concerns related to an incumbent MDR provider by assessing the effectiveness of the MDR provider’s detection technologies, rules and operations in a systematic manner. |
| Client concerns addressed | MDR service degradation that had resulted in:
|
The combination of our experience, technical insights, and wider industry knowledge combine to form the basis of our SOC testing and validation services. It is, however, our focus on threat intelligence that makes this service so valuable and unique.
It has never been more important to test existing SOC and MDR services. Adopting a robust testing approach will ensure the accuracy and effectiveness of this critical service area. At Thomas Murray, we accurately simulate both common and industry-specific threat actors in a manner that is aligned to the client’s risk appetite.
Cyber Risk
We bring the best of our collective experience, energy and creative power to fiercely safeguard our clients and fortify their communities.
Insights

Top 5 Things Investors and Allocators Should Look for in Technologies Streamlining Operational Due Diligence
Our work at the intersection of institutional risk and market infrastructure has shown us what makes ODD technology truly impactful.

M&A Cybersecurity Red Flags: A practical checklist for deal teams
Find out about the hidden liabilities that kill deals

AI Has Moved the Asset Safety Goalposts
The AI threat era has changed the meaning of asset safety for financial institutions.

What is the ASFA Guidance Note and Why Does it Affect Due Diligence?
Learn about the importance of tailored due diligence.

