In an era where cyber threats are ubiquitous and increasingly sophisticated, having a robust cyber incident response plan (CIRP) is indispensable for any organisation. However, the process of developing this plan is as critical as the finished document itself.
This journey to creating a CIRP, whether on your own or with expert support, fosters a deeper understanding of the organisation, strengthens organisational defences, and ensures a state of preparedness that a pre-packaged plan simply cannot provide.
What is a cyber incident response plan?
A CIRP contains the documented approach for responding to a cyber incident. It should contain the strategic and tactical steps an organisation will follow when a cyber incident occurs.


At its core it should:
- outline roles and responsibilities;
- define communication strategies:
- set out specific actions to contain the threat and mitigate against any damage it may have caused;
- describe how to eject the threat from the environment; and
- prepare the business to recover data and restore normal operations.
The journey
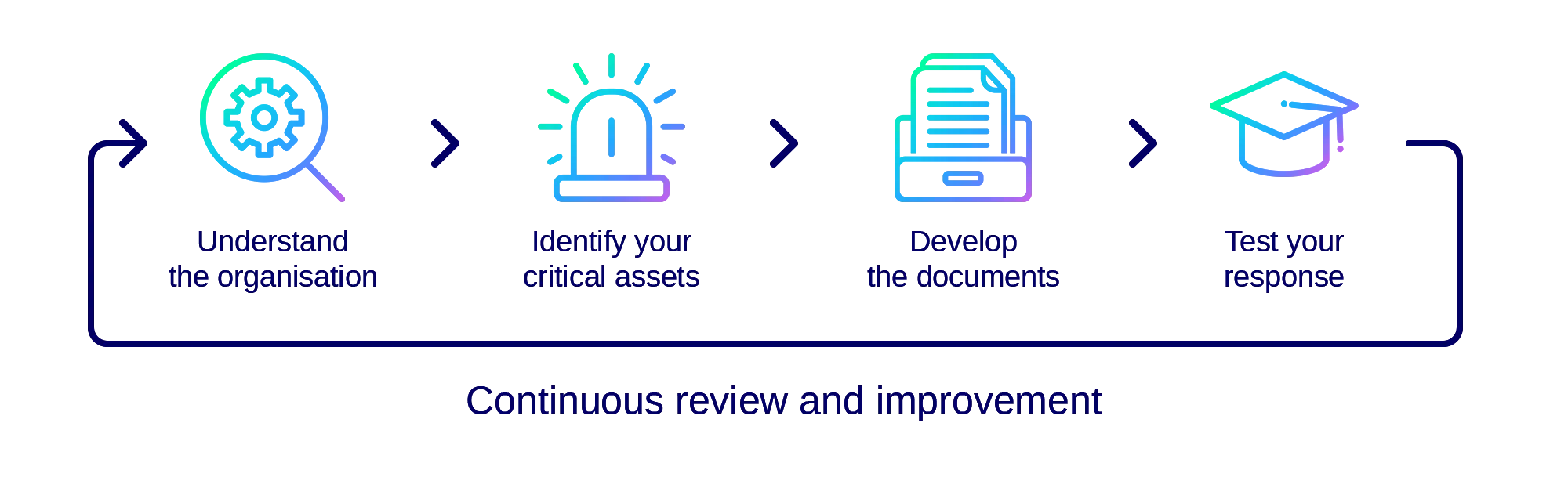
The process of creating a CIRP should follow four general phases:
- Understand the organisation;
- Identify your critical assets;
- Develop the documents; and
- Test your response.
1. Understand the organisation
Creating an effective CIRP necessitates a thorough understanding of the organisation. The obvious aspect of this is the technology in use, the data the organisation holds and the capability it has to respond. But a CIRP cannot solely focus on the technical aspects of a response – it must also consider the needs and culture of the business, and its legal and regulatory obligations alongside its risk appetite.
A CIRP should be developed in collaboration with stakeholders from technical operations, legal, HR, communications, and marketing to name a few. Ensuring that every part of the business has the opportunity to contribute meaningfully to the CIRP’s development helps foster a culture of security. This cultural shift towards heightened awareness and responsibility can be as beneficial as the plan itself.
2. Identify your critical assets
Once you understand the needs and culture of the business, and what it needs to function at a business level, you then need to delve into the technical environment to identify what you need to protect.
The most obvious approach is to look at the critical technical assets, those systems and servers without which the business could not continue to function. In a traditional environment these could be your domain controllers, critical application servers, and file systems.
However, as more business move to SaaS platforms and hybrid or cloud-first models these may not be as easy to find or as obviously in need of protection. Consider where your organisation has critical or sensitive data, and which third parties manage the underlying systems that provide access.
Taking a detailed review of these areas will naturally take you to a deeper level than a CIRP and into developing dedicated playbooks. This is an opportunity to carefully consider the individual requirements of an incident response in each of these platforms or environments, and shaping your response actions accordingly.
3. Develop the documents
Once organisational understanding is matured and threats are understood, the actual processes for the CIRP should be developed and documented.
Various standards and frameworks exist to help guide the documentation process and ensure that key aspects are considered. The most well-known standard, 800-61 from NIST, provides a comprehensive set of recommendations for documenting a mature incident response plan. In addition, the NCSC provides a starting point for organisations just starting out on their journey.
Whichever framework or approach is used, an iterative approach should be taken to developing the documentation. This means, in effect, stepping through the incident response process from beginning to end in a logical flow and documenting each step. By taking this approach you ensure all angles are covered, and that you have ample opportunity to consider the nuances of every action.
4. Test your response
After embedding the CIRP in your organisation, you need to ensure that it meets the needs of the business and facilitates a robust response to any cyber security incident. You also need to ensure that the internal and external stakeholders understand their roles and responsibilities, so that it becomes “muscle memory” to a certain extent.
A tabletop exercise planned and executed by experienced incident responders provides the best opportunity to stress-test your response in a safe and controlled environment. These exercises help identify gaps and weaknesses in the plan, and opportunities for improvement. The practical simulation prepares the team to respond effectively when a real incident occurs.
Continuous review and improvement
Your CIRP is a living document and should not be something that is only called upon for the annual exercise and review cycle or when an incident occurs. By taking the time to foster that culture of security you can embed the concept of regularly updating the CIRP in response to new threats, technologies, regulations, and business changes within the organisation.
Wrapping up
While having a completed CIRP is essential, the process of developing that plan is equally, if not more, important.
It is through this process that information security teams can gain a deep understanding of their organisation, foster a culture of security, enhance communication and coordination, and build a foundation for continuous improvement. The path to creating an incident response plan equips an organisation with the knowledge, skills, and resilience needed to effectively tackle cyber threats, making the process a critical component of an overall cyber security strategy.
Cyber Risk
We bring the best of our collective experience, energy and creative power to fiercely safeguard our clients and fortify their communities.
Insights

Ransomware at Europe’s Airports: Case for Community-Driven Third Party Risk Management
The recent ransomware attack on Collins Aerospace’s Muse software, which brought chaos to airports across Europe, serves as a stark reminder of a critical gap in how organisations approach Third Party Risk Management (TPRM).

JLR Cyber Attack: What it Means for Private Equity, Credit, and Equity Investments
From the iconic E-Type Jaguar to images of the late Queen driving modern Range Rovers on her estate, JLR has long held a uniquely British place in the national consciousness, even under Tata ownership. The incident has affected the owners of the business, the supply chain, and customers, and offers learnings for the Private Equity (PE) industry.

Impact of Cyber and Operational Resilience on Private Equity and Their Portfolio Companies
Implementing cyber and operational resilience measures is a strategic imperative for PE firms and their PortCos, enabling them to reduce the impact of cyber risks on asset valuations.

How Private Equity Leaders Turn Cyber Security Investment into Competitive Advantage
Leading firms are discovering something counterintuitive: investing in cyber security creates advantages worth far more than just protection.

