On 17 March 2026, Thomas Murray hosted the third in a series of risk briefings, detailing developments in the Middle East region over the past week. A number of these developments are detailed below.
The Middle East is now at a critical juncture, given the ongoing war. In addition to the current geopolitical landscape, The Gulf Cooperation Council (GCC) has overseen a decade of digital transformation in the region - underpinned by Saudi Vision 2030, Qatar National Vision 2030, and UAE's Digital Economy Strategy. This is creating some of the world's most connected and data-intensive economies. But, with this new connectivity has come heightened exposure.

Against a backdrop of active regional conflict and state-sponsored cyber campaigns, regulators across the GCC have now moved from guidance to mandate. In 2025 alone, GCC member states introduced or materially updated their national cybersecurity frameworks. The direction of travel is clear: cyber resilience is now a pillar of sovereign stability, not a back-office IT concern.
Why this matters now
Cyberattack campaigns began within hours of Operation Epic Fury, and as shown by Thomas Murray’s attack data from 27 February to 15 March 2026, this has been sustained at an elevated tempo rather than spiking and collapsing (the peak single-day volume was 88 incidents on 6 March).
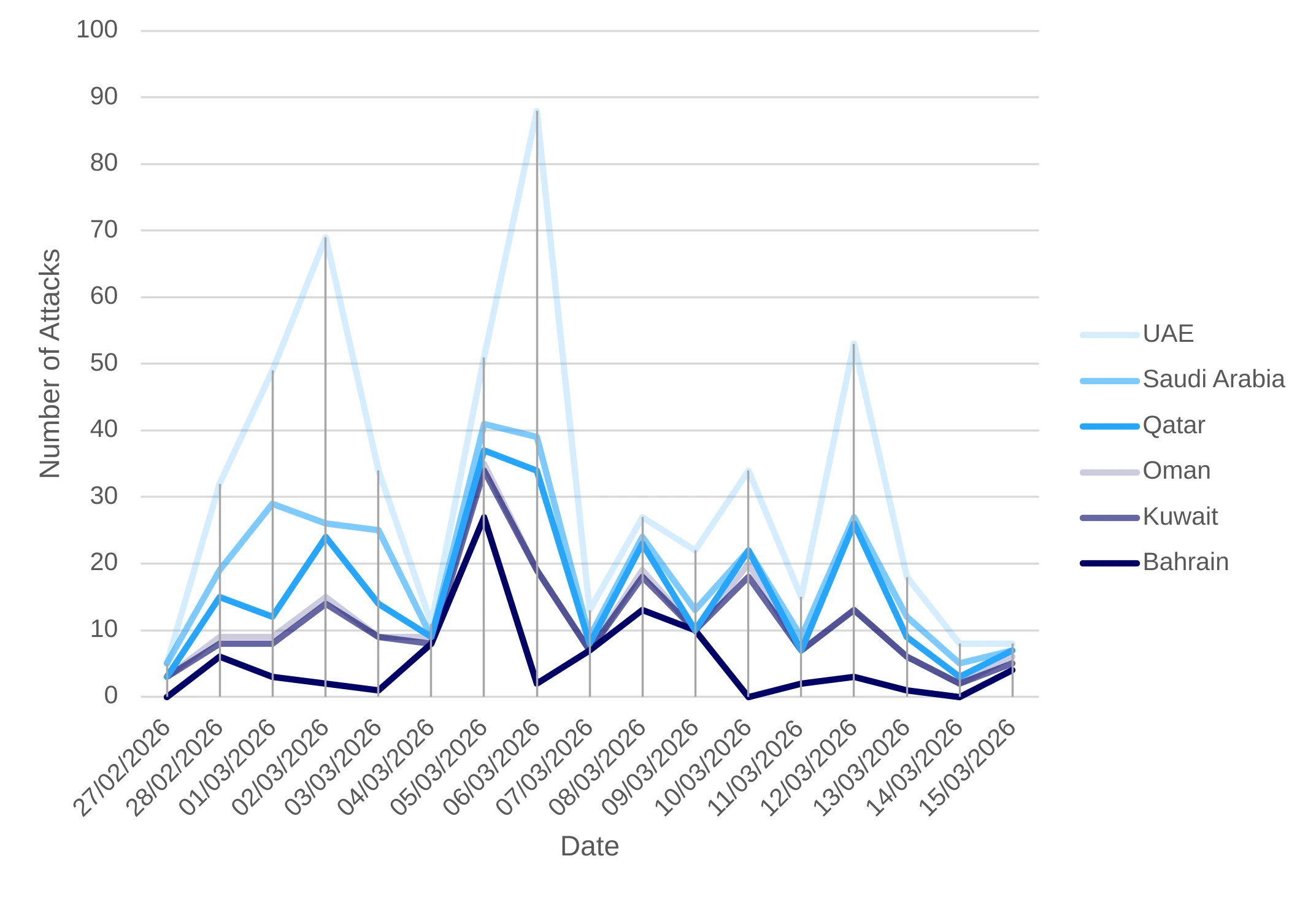
Attack Volume
198 of 550 incidents targeted government organisations, reflecting the dual objective of symbolic disruption (attacking state legitimacy) and intelligence collection. IT Services and MSPs are low in volume (8) but have been assessed as the highest-consequence category: compromise enables downstream access to multiple government and critical infrastructure customers simultaneously.
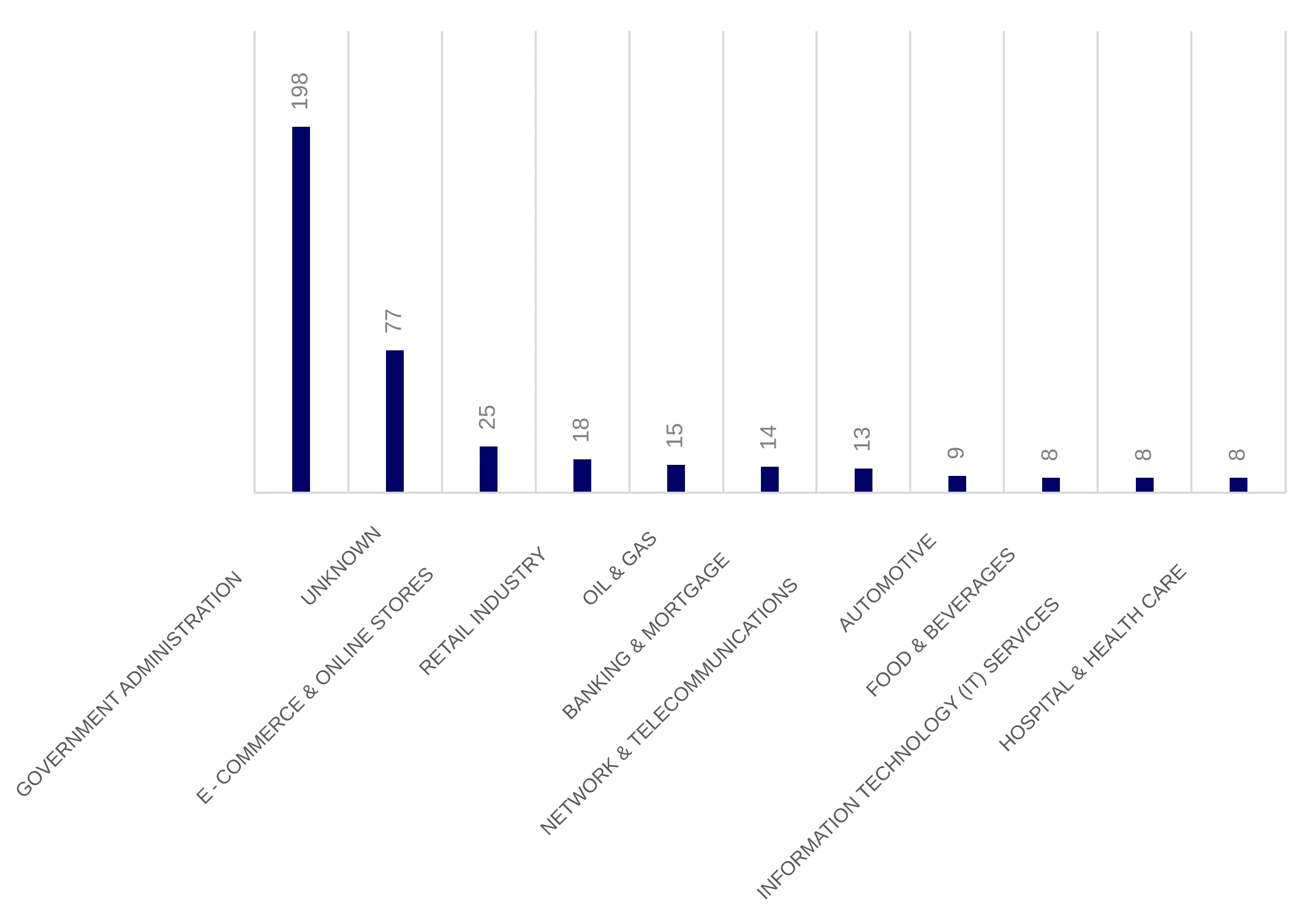
Top 10 Sectors targeted across the GCC
The UAE accounts for 220 of 550 incidents (40%) and is dominated by defacement (134 of 220). Every other GCC state is DDoS-dominated. This suggests the UAE attracts a broader opportunistic hacktivist population, alongside Iran-aligned groups - reflecting its Abraham Accords status and symbolic value as a normalisation target.
Bahrain accounts for 90 incidents, the third highest, despite being the smallest GCC state by population. 76 of 90 are DDoS attacks. The US Navy's Fifth Fleet at NSA Bahrain is likely the primary driver here. 313 Team (35) and Hider_Nex (25) account for two-thirds of all Bahrain incidents.
| Country | Total Incidents | % of Total | DDoS | Defacement | Other |
|---|---|---|---|---|---|
| UAE | 220 | 40.0% | 48 | 134 | 38 |
| Kuwait | 100 | 18.2% | 73 | 9 | 18 |
| Bahrain | 90 | 16.4% | 76 | 0 | 14 |
| Qatar | 70 | 12.7% | 44 | 7 | 19 |
| Saudi Arabia | 60 | 10.9% | 16 | 17 | 27 |
| Oman | 10 | 1.8% | 4 | 0 | 6 |
| TOTAL | 550 | 100% | 261 | 167 | 122 |
Industries facing the greatest exposure include energy and oil infrastructure, financial services, aviation, telecommunications, defence, and IT service providers. Critically, organisations without direct ties to conflict zones are not immune - collateral targeting, supply-chain vulnerabilities, and opportunistic exploitation of third parties are well-documented attack vectors.
The regulatory response is directly calibrated to this reality. Frameworks across the region increasingly mandate board-level accountability, mandatory incident reporting, third-party risk governance, and tested business continuity - precisely the controls that differentiate organisations that withstand disruption from those that do not.
The regulatory landscape
What was once a patchwork of cybercrime laws and sector-specific guidance has matured into a sophisticated, multi-layered regulatory architecture. The trend is consistent across all jurisdictions: regulations are moving from principles to prescriptive controls, from voluntary to mandatory, and from IT teams to boardrooms.
The following table summarises the primary regulatory frameworks, responsible authorities, and focal areas across each jurisdiction.
| Country | Key Regulator | Key Regulations / Frameworks |
|---|---|---|
| UAE | UAE Cyber Security Council; TDRA; CBUAE; ADGM; DIFC | NESA IAS (188 controls); UAE Cybersecurity Strategy 2024–25; Federal Decree-Law No. 45/2021 (PDPL); ADGM Cyber Risk Management Framework (2025); Dubai Cyber Security Strategy |
| Saudi Arabia | NCA; SAMA; SDAIA; CITC | NCA ECC-2:2024 (Essential Cybersecurity Controls); SAMA Cybersecurity Framework; PDPL (2021, enforced 2024); NCA OTCC (OT Controls); National Cybersecurity Strategy aligned with Vision 2030 |
| Qatar | NCSA; QCB; MOICT | National Cyber Security Strategy 2024–2030; QCB Cybersecurity Framework; Data Protection Law (2016, enhanced 2025); Q-CERT Critical Infrastructure Programme; Digital Government Strategy 2023–25 |
| Bahrain | NCSC; CBB; TRA | National Cyber Security Strategy; Cloud First Policy; PDPL (GDPR-aligned); CBB Cybersecurity Framework; Cybercrime Prevention Law (2014) |
| Oman | NCSC Oman; TRA; CBO | National Cybersecurity Strategy; Cloud Computing & Data Centre Regulation (Ministerial Decision No. 1152, 2024); Cybercrime Law; CBO Operational Risk Guidelines; Personal Data Protection Law |
| Kuwait | NCSC Kuwait; CBK; CITRA | CBK Cyber & Operational Resilience Framework – CORF (Dec 2025); NCSC Data Classification Framework – Decision No. 1/2025; National Cybersecurity Center Decree No. 37/2022; Cybercrime Law (2015); Kuwait Vision 2035 ICT Strategy |
The importance of broader resilience strategies
Organisations that embed compliance into their broader resilience strategies reduce risk exposure, recover faster from incidents, and demonstrate to partners and regulators that security is a strategic priority, not an afterthought.
The regulatory journey across the GCC is accelerating, not plateauing. Regulatory standards will continue tightening, with cyber risk increasingly embedded into financial and licensing decisions, and procurement. Organisations achieving mere adequacy today face the prospect of perpetual catch-up.
The most resilient organisations - those that will navigate the current geopolitical turbulence and emerge with their operations, reputations, and stakeholder trust intact - are the ones treating resilience not as a regulatory obligation but as a strategic capability, built deliberately, tested regularly, and owned at the highest levels of leadership.
The frameworks are in place. The threats are real. The question is no longer whether to invest in resilience - it’s whether you will have done so before the next major disruption arrives.
Thomas Murray risk briefings
The latest Thomas Murray Middle East conflict risk briefing took place on 17 March 2026.
If you were unable to attend, you can access the deck here or watch the 30-minute recording here.

Compliance Digest Newsletter
Subscribe to Compliance Digest and stay up to date with regulations affecting the finance sector.